Smart Grids and Cybersecurity: Risks and Countermeasures
September 18, 2025
Introduction
Energy powers every part of modern society. Homes, hospitals, transport, and businesses depend on stable and reliable electricity. The traditional electricity grid was once isolated and simple. Today it is digital, connected, and intelligent.
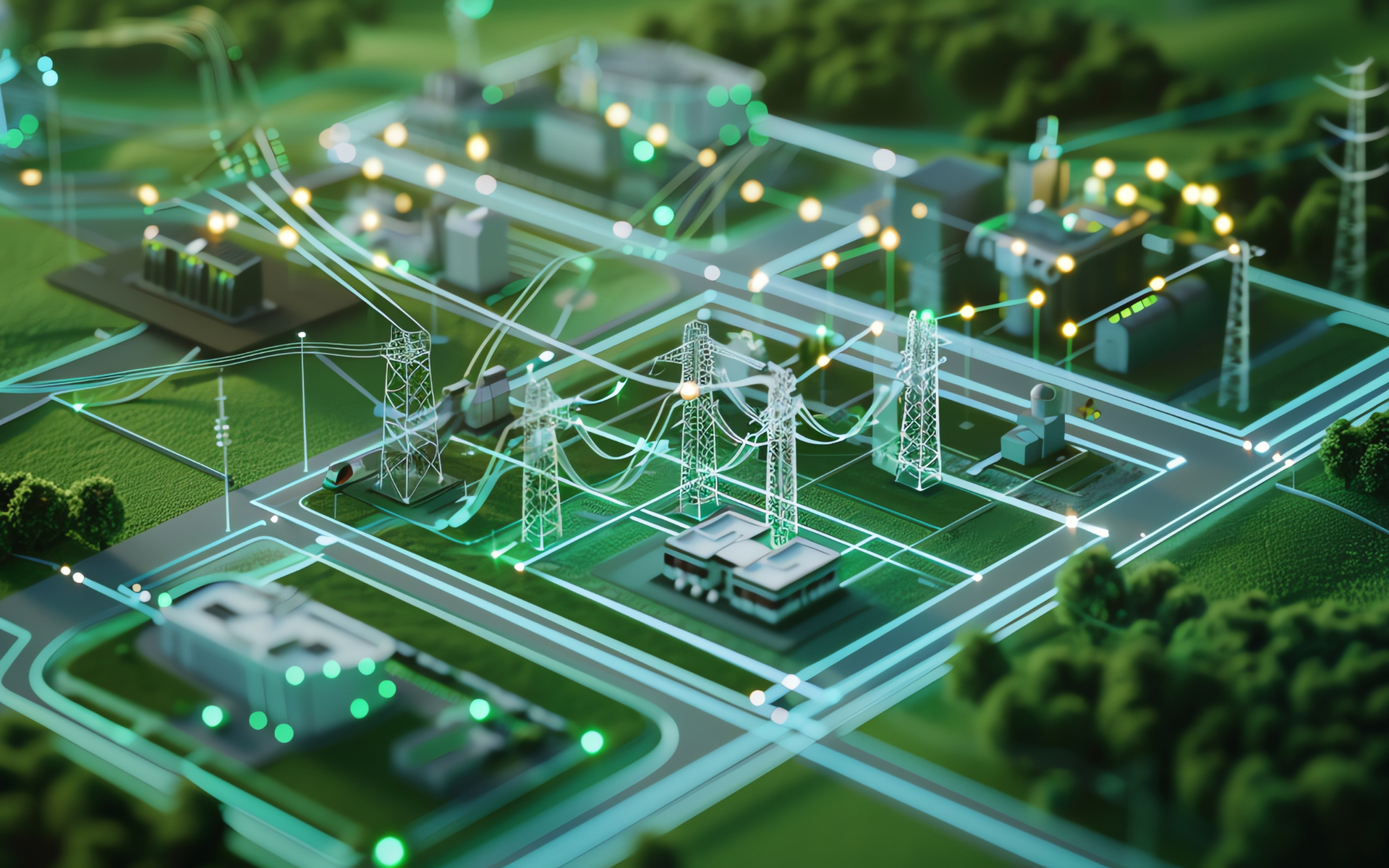
This is the smart grid. A smart grid uses sensors, software, and connected devices to manage electricity in real time. It balances supply and demand, supports renewable energy, and provides detailed data on usage. This innovation increases efficiency and reduces waste. It also introduces new security risks.
Cyber threats against critical infrastructure are rising. Attacks on energy systems have grown more frequent and more damaging. Smart grids are attractive targets for cybercriminals, nation states, and activist groups. A successful attack could stop power supplies, damage trust, and harm economies. This blog is for businesses, IT teams, students, policymakers, and individuals who want to understand smart grid risks. You will also learn the steps you should take to improve security.
A smart grid is more than a collection of wires and power plants. It is a complex digital system connected to homes, offices, and devices. A simple example is the smart meter in your home. The meter communicates with your energy provider, sending real-time data about your usage. This helps manage supply, but it also creates an entry point for cybercriminals if not properly secured. The rise of these devices makes smart grid cybersecurity urgent.
What Are Smart Grids and Why They Matter Now
A smart grid is the digital upgrade of the traditional electricity grid. In the past, energy flowed one way from a power station to consumers. Monitoring was basic and slow. In a smart grid, energy and data flow both ways. Sensors report demand, faults, and performance instantly. Operators can react quickly. Households and businesses can also generate energy, such as solar power, and feed it back into the grid.
This system improves efficiency. It lowers costs by reducing waste and outages. It supports renewable energy, which is less predictable than fossil fuel supply. The smart grid is essential for achieving climate goals. It is also vital for managing growing populations and expanding urban centres.
The difference between traditional and smart grids lies in data. A smart grid collects vast amounts of information every second. This data is processed and used to balance supply and demand. A household with a smart meter is an example. The meter records energy use and sends data to the supplier. The supplier can adjust supply based on thousands of similar inputs across the country.
Smart grids matter now because demand for electricity is growing. Electric vehicles, smart homes, and new industries all increase pressure on the system. Governments and regulators are pushing for renewable energy and efficiency. Smart grids are the only way to manage this complexity. At the same time, more devices connected to the grid increase the attack surface for cyber threats.
Common Cybersecurity Threats Facing Smart Grids
Smart grids face unique cybersecurity risks. Each part of the system is a potential target. Threats include malware, ransomware, insider actions, IoT vulnerabilities, and supply chain attacks.
Malware and ransomware can infiltrate control systems. In 2015, hackers attacked the Ukrainian power grid using malware. They gained access to control systems and shut down substations. Over 200,000 people lost power for several hours. This was a clear warning that energy systems are vulnerable.
Insider threats are another risk. Employees or contractors with access to systems may act maliciously or make mistakes. A disgruntled employee could steal data or sabotage operations. A poorly trained worker could introduce risks by clicking on a phishing email.
IoT devices such as smart meters are weak points. These devices are often low cost and produced at scale. Security is not always prioritised in design. Attackers can exploit these devices to gain entry to the wider network. Once inside, they can move through systems and cause damage.
Supply chain risks are growing. Energy companies rely on vendors for software, hardware, and services. An attacker may target a vendor with weaker defences. By compromising the vendor, they can access the utility. This type of attack is harder to detect and often devastating.
Smart grids are complex networks. Each part is connected. An attack on one part can spread quickly. This makes defence difficult and requires constant vigilance.
Consequences of Cyberattacks on Smart Grids
Cyberattacks on smart grids carry serious consequences. Power outages disrupt daily life. Hospitals depend on electricity for life support equipment. Transport networks stop without power for signalling and control. Businesses lose money when systems shut down.
Financial damage extends beyond outages. Recovery from attacks is costly. Restoring systems, replacing equipment, and compensating customers requires huge resources. Insurance costs rise and reputations suffer.
Public trust is fragile. People expect electricity to be available at all times. An attack that cuts power undermines confidence in providers and governments. Trust once lost is difficult to rebuild.
Data theft is another concern. Smart grids collect vast amounts of personal and business data. If attackers access this data, they can use it for fraud or espionage. Stolen data erodes privacy and increases the risk of identity theft.
The consequences are not limited to one country. Energy systems are interconnected. An attack in one region can affect others. This global interdependence raises the stakes. Defending smart grids is not optional. It is essential for national security and public safety.
Countermeasures and Security Strategies
Protecting smart grids requires a layered approach. No single solution is enough. Security must be built into every part of the system.
Patch management is critical. Attackers often exploit known vulnerabilities. Regular updates close these gaps. Monitoring systems for unusual behaviour helps detect intrusions early. Rapid detection reduces damage.
Training for employees reduces insider risks. Staff must understand phishing, password hygiene, and reporting procedures. A well informed workforce is a strong defence.
Incident response planning prepares organisations for attacks. Plans outline roles, communication, and recovery steps. Practising scenarios ensures readiness. A fast and coordinated response limits impact.
Industry frameworks provide guidance. The National Institute of Standards and Technology (NIST) offers a Cybersecurity Framework. In the UK, Cyber Essentials provides a government-backed
scheme for basic security controls. Adopting these frameworks strengthens resilience.
At Cybergen, we recommend continuous monitoring of systems. Regular penetration testing reveals weaknesses before attackers exploit them. Encryption protects data in transit and at rest. Multi factor authentication secures access. Supplier assessments reduce supply chain risks.
Practical Steps for Organisations and Individuals
Organisations must act now to reduce risk. Regular penetration testing identifies weaknesses. Addressing these gaps improves security before attackers exploit them.
Encryption is essential. Data must be protected during transmission and while stored. Multi-factor authentication secures access to systems. Strong access controls limit insider threats.
Supplier risk must be checked. Vendors and contractors should meet strict security standards. Contracts should include security requirements.
Training employees builds awareness. Phishing remains a common attack method. Staff who recognise threats reduce risk. Training must be continuous to stay effective.
Individuals also play a role. Households with smart meters should follow basic cyber hygiene. Secure home Wi Fi networks with strong passwords. Keep devices updated. Report suspicious activity to energy providers.
Summary
Smart grids are essential for modern energy needs. They improve efficiency and support renewable energy. They also introduce serious cybersecurity risks. Attacks on smart grids threaten lives, economies, and national security.
The threats are real and growing. Attackers target control systems, employees, IoT devices, and supply chains. The consequences include outages, financial damage, loss of trust, and stolen data.
Defence requires action. Organisations must adopt layered security. They must follow frameworks such as NIST and Cyber Essentials. They must invest in training, monitoring, and incident response. Individuals must also follow good practices at home.
References
Anderson, R. and Fuloria, S., 2010. Who controls the off switch. Proceedings of the First IEEE International Conference on Smart Grid Communications, pp.96-101.
Chen, T.M., 2010. Smart grid security: Threats and countermeasures. IEEE Network, 24(1), pp.38-45.
Li, F., Luo, B., and Liu, P., 2010. Secure information aggregation for smart grids using homomorphic encryption. First IEEE International Conference on Smart Grid Communications, pp.327-332.
NIST, 2018. Framework for Improving Critical Infrastructure Cybersecurity. National Institute of Standards and Technology.
UK Government, 2025. Cyber Essentials. Available at: https://www.cyberessentials.ncsc.gov.uk
Zetter, K., 2016. Inside the cunning, unprecedented hack of Ukraine’s power grid. Wired.
Ready to strengthen your security posture? Contact us today for more information on protecting your business.
Let's get protecting your business
Thank you for contacting us.
We will get back to you as soon as possible.
By submitting this form, you acknowledge that the information you provide will be processed in accordance with our Privacy Policy.
Please try again later.
Cybergen News
Sign up to get industry insights, trends, and more in your inbox.
Contact Us
Thank you for subscribing. It's great to have you in our community.
Please try again later.
SHARE THIS
Latest Posts









